For a variety of reasons, a lot of companies are moving to an Agile, DevOps Culture, Continuous Integration and Delivery/Deployment (CI/CD) model. These transformations rely on a variety of tools, including open source. A lot of organizations also use open source tools and libraries to develop their applications and in order to ensure security, these libraries need to be actively managed and scanned for potential vulnerabilities. As applications get more complex, the number of these open source libraries that development and security teams have to manage increases.
In the first part of this blog series, I will tell you about a tool that can help development teams, security teams, and organizations as a whole in identifying and mitigating vulnerable open source libraries within their applications. It is called Nexus Lifecycle and is Sonatype’s new addition to their Nexus suite that scans application binaries for known vulnerabilities in open source libraries.
In my next blog, I will talk about how Coveros helped an enterprise client implement Nexus Lifecycle along with an upgrade of Nexus Pro Repository with minimal impact and downtime.
Just like Nexus Firewall and Nexus Audit, Nexus Lifecycle is powered by Nexus IQ server. However, it comes with some additional features that are not available in the other Nexus tools. Nexus IQ server is the brain of the operations. This is where you setup your customizable policies which will decide which open source libraries are acceptable by the organization and which ones are not. You can also have different policy actions setup for different stages of your software development lifecycle. Nexus IQ integrates nicely with Nexus Pro Repository and shows the health of your repository according to the policies you have in place. However, I think the best feature of Nexus Lifecycle is that you can integrate Nexus IQ with popular development tools such as:
- Integrated development environments (IDE) like Eclipse and IntelliJ
- Automation build tools like Jenkins and Bamboo
- Quality monitoring tools such as SonarQube.
I like the plugin for IDEs because it provides the ability to detect vulnerabilities early in development (see Figure 1).
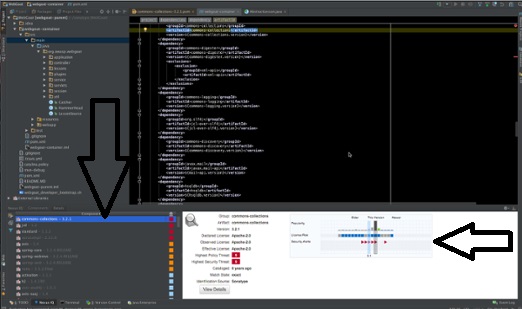
This follows the “shift-left” paradigm where companies want to deliver quality from day one and detect any defects early in the software development lifecycle where the cost of mitigating such defects is cheaper.
Lifecycle also offers a great GUI and dashboard (see Figure 2) so that people from different teams with different technology skill sets can see what is going on. Nexus IQ has different levels within the organization where policies can be applied, starting from the root of the organization all the way to the application level. This is particularly useful when you want some applications to have more or less strict policies for any reason.
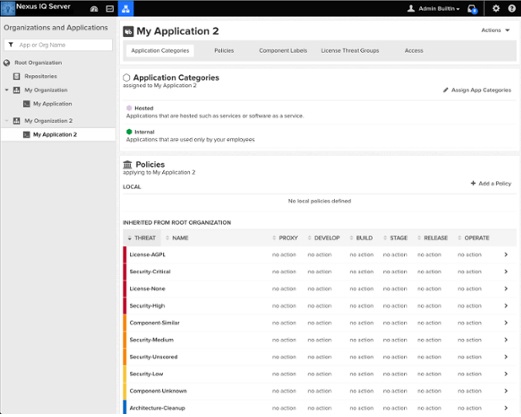
Once you setup policies, configure Nexus Pro repository, install and configure plugins in Jenkins and Eclipse, then you can start checking your applications against those policies. You can do that through the Nexus IQ GUI manually, automatically through Jenkins, or directly from your IDE when you try to build it locally. If any of your libraries fail against any of the policies, then several things can happen based on how you configured your IQ server:
- Open source libraries could be quarantined
- You could fail your build and/or send a warning message
- Your local build fails to pull from the proxy repo
After completing a manual scan through Nexus IQ or automatic scan from Jenkins, the security team can review reports and evaluate which applications comply or do not comply with all the policies in place (see Figure 3). They can also decide to unquarantine certain libraries and accept the risk for the organization. One flaw that we found is that Lifecycle’s reporting and dashboards can only display 100 items but that is a topic for another blog.
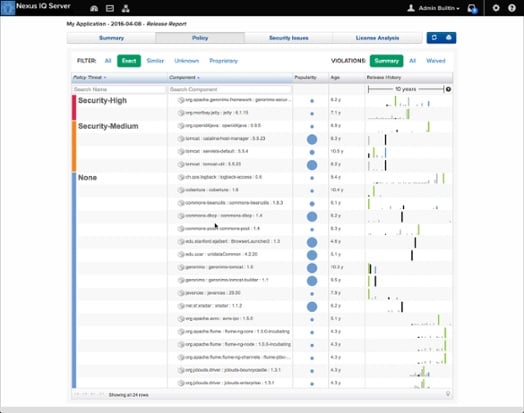
Overall I think this tool has a lot to offer, especially for organizations that have mature Agile teams with automation in place. You can have Nexus IQ as an additional quality gate which will programmatically fail, warn, or push your code through the pipeline.




One thought to “Sonatype’s New Nexus Lifecycle Helps Teams Migrate Open Source Libraries”
Pingback: Sonatype’s New Nexus Lifecycle Helps Teams Migrate Open Source Libraries - Coveros